Data Sovereignty & Security
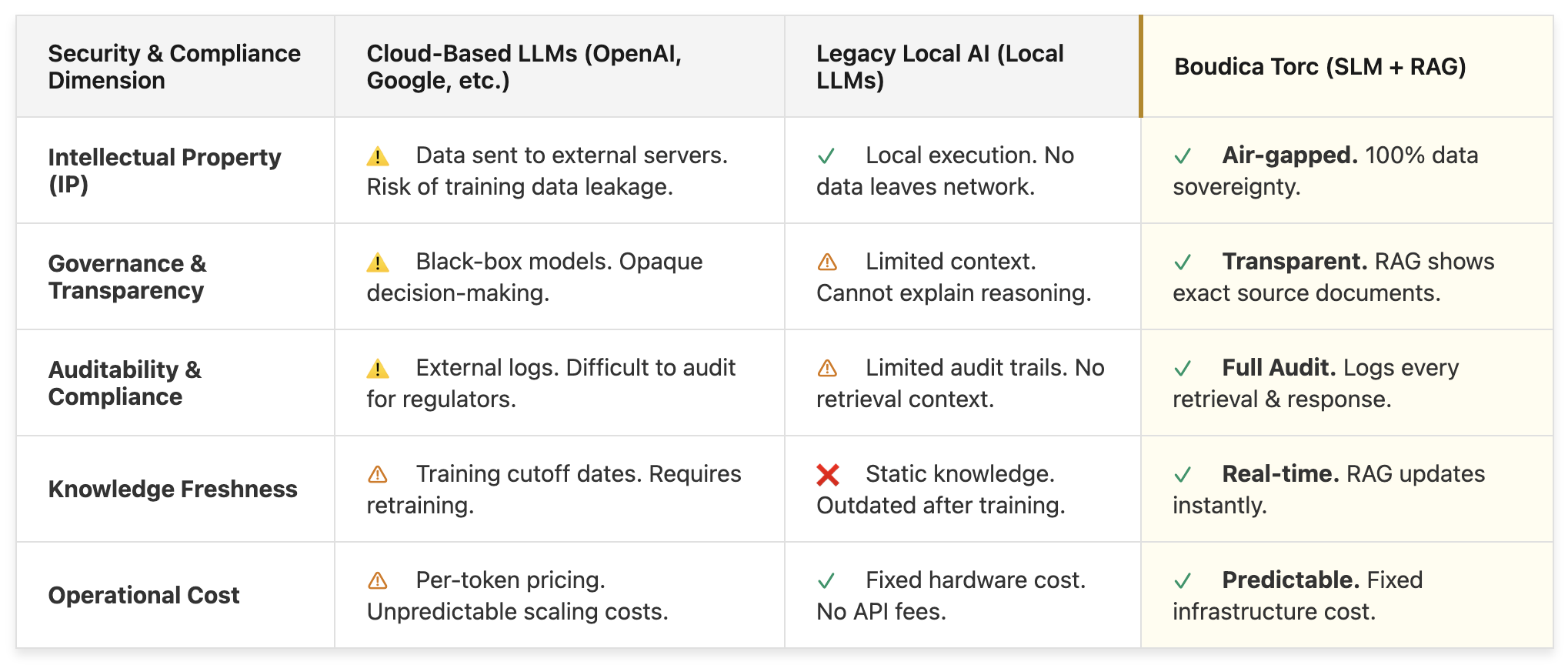
Boudica Torc is developed with complete corporate governance controls, ensuring your IP is fully audited and never leaves your control.

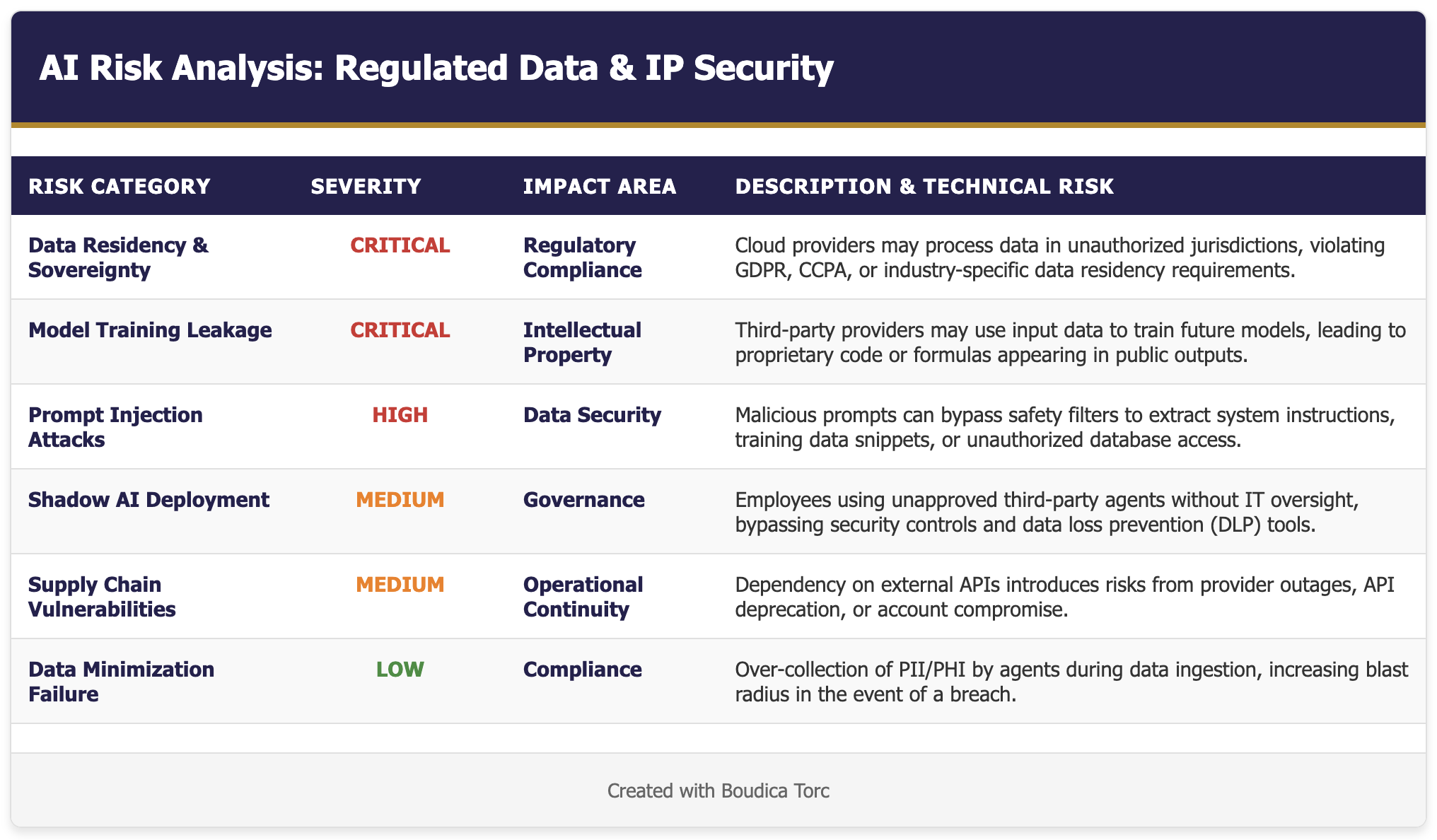
Every time you prompt a cloud-based LLM, you are sending your Intellectual Property & ideas out of your secure environment. This both risks your data, and means you cannot audit exactly how it has been used.
Never Risk Your IP.
Boudica Torc is engineered for organizations that cannot compromise on data privacy or regulatory compliance. It provides a complete "air-gapped" architecture that ensures sensitive information never leaves your controlled environment.
Own Your Own Intelligence.
Key Torc Features
On-Premises Deployment
The entire stack runs on your own hardware. This eliminates third-party data processing risks with IP never leaving your secure control.
User Permission Controls
Boudica Torc implements role-based access control (RBAC) filters directly at the retrieval layer to ensure data sovereignty. This system allows organizations to enforce security boundaries by restricting access to specific specialists or conversation memories based on user permissions.
Identity Integration
Native integration with Keycloak OIDC/SAML ensures that AI access is governed by your existing corporate security policies.
Audit & Compliance
Every interaction is logged locally, providing a complete audit trail for regulatory reporting and security forensics.
Key AI Sovereignty Use Cases
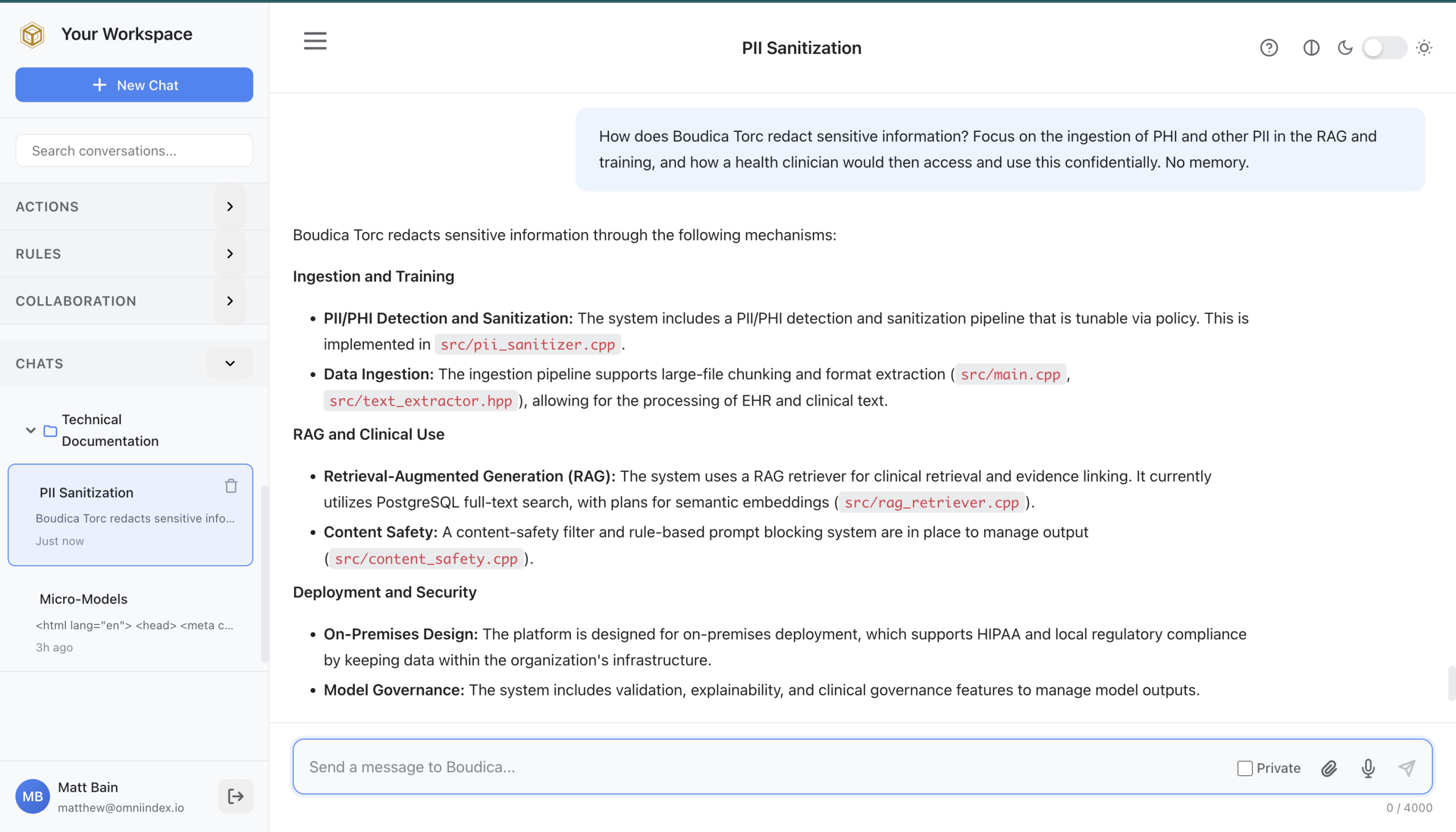
Healthcare & Life Sciences
Risk: HIPAA violations and loss of patient confidentiality. Research IP leakage to competitors.
Boudica Solution: HIPAA-compliant architecture. RAG allows clinicians to query patient records without exposing data to the internet.
Financial Services & Banking
Risk: Regulatory non-compliance (GDPR, Basel III) if customer data is processed by third-party providers.
Boudica Solution: Complete data isolation. All PII remains within the bank's secure perimeter. Full audit trails for regulatory inquiries.
Defense & National Security
Risk: State-sponsored attacks on cloud APIs. Data exfiltration via API calls.
Boudica Solution: Air-gapped deployment. No internet connectivity required. Complete control over model weights and training data.
All rights reserved © 2026 OmniIndex

